I have had a series of posts recently about various, supposedly responsible, Social websites asking for my username and passwords (email), and another post about not so trustworthy sites asking for Live Services passwords. I had resolved to only be concerned about sites that were clearly not taking advantage of the OAuth security pattern, however, it is quite difficult to explain to a layman if a site is using OAuth or taking short cuts of storing your password, logging in and doing some kind of screen scraping. I hope to address this here.
Why do we even need something like OAuth? Well if you are, like me, a user of the something like Live services, but you would love to be able to import all your contacts from a social network like LinkedIn. You have a couple of options, hope that LinkedIn allows you to export the contacts in some common format (csv, xls, etc) and also hope that Windows Live offers a compatible import solution … or … you need an Open secure API which both services can comprehend, vis-a-vis OAuth (I will not go into the details of the OAuth pattern, except to say that it overcomes the need to send user id and password with every request sent to a third party, like BasicAuth).
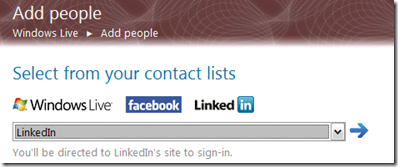
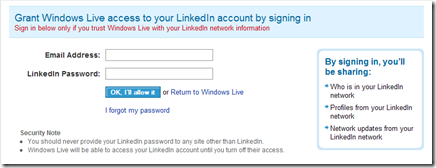
In short when a site is responsible enough to employ the OAuth open protocol you can gain access to secure areas (contacts, photos, etc) of other sites without spreading your password everywhere. A good example of this pattern can be seen at work in the Windows Live Services. I go through the steps of selecting the import process from LinkedIn, as shown below.
This is the really important part here! After clicking next I am redirected to the LinkedIn web site for authorization. What you should not be doing at this point is adding your LinkedIn credentials into the Windows Live site. This is always a bad idea! To be clear I trust both LinkedIn and Windows Live, I just do not believe they need the keys to each others houses.
Any system that teaches users that it is ok to put passwords from one site into another is really doing us all a disservice, this password Anti Pattern teaches people that it is ok to give away your password. This bad habit ensures that people will be more likely to be caught in Phishing scams the world wide web over. Many social networks have spread like this and LinkedIn is as guilty as any of them.
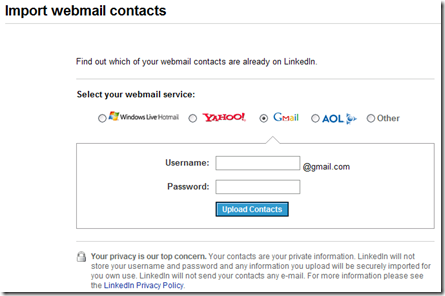
For me the design of this LinkedIn import page is really problematic. While it appears to redirect authentication for Windows Live and Yahoo, for Gmail, AOL and the Others options it relies on you putting user names and passwords directly into the LinkedIn site.
I am sure that LinkedIn is being above board and responsible with my information (am I) but this pattern is doing the overall security of the web no good. They are teaching a whole generation of Social network users that this type of password sharing is ok.
What is more confusing is that AOL and Gmail appear to have OAuth implementations (AOL OpenAuth, Google AuthSub) yet LinkedIn seems to disregard this and teach bad habits to its users.
Hopefully in a future post I will go through some code that complies with the OAuth pattern.
Comments are closed.